Macos 10.14.6 This Software Is Not Supported
About Apple security updates
- Macos 10.14.6 This Software Is Not Supported Video
- Macos 10.14.6 This Software Is Not Supported Free
- Macos 10.14.6 This Software Is Not Supported Youtube
- Macos 10.14.6 This Software Is Not Supported Iphone
For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
- On August 1, 2019, Apple released a supplemental update of macOS Mojave 10.14.6. According to Apple, this update includes a fix for an issue “that may prevent certain Macs from waking from sleep.
- Jul 02, 2020 Apple has a pretty good track record of providing software updates and support to their devices for years, but naturally not all Macs will officially support macOS 11 Big Sur. Whether you own a MacBook Pro, MacBook Air, MacBook, iMac, Mac mini, or Mac Pro, read on to figure out which Macs are able to run macOS Big Sur.
Apple security documents reference vulnerabilities by CVE-ID when possible.
Aug 26, 2019 Apple has released another new supplemental update to macOS Mojave 10.14.6. The supplemental software update includes bug fixes, security enhancements, and performance improvements, and is therefore recommended for all Mac users running MacOS Mojave to install. The new supplemental update will bring macOS 10.14.6 to build 18G95.
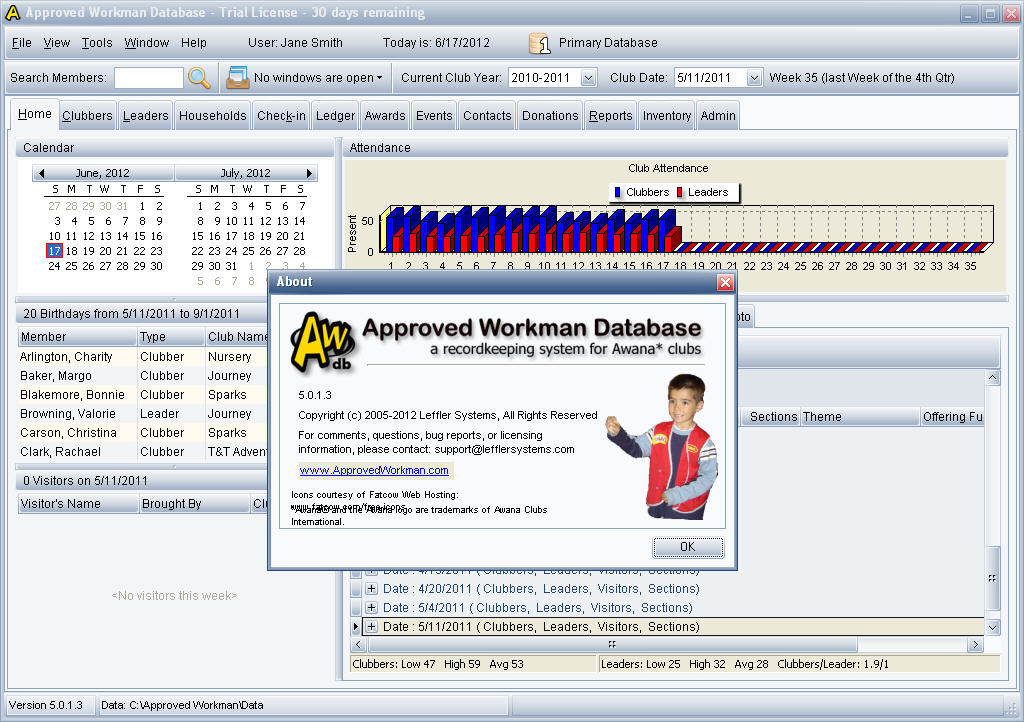 Leaders/listeners can use the Web App on their smartphones, tablets, Mac or Windows PCs to record clubber attendance and mark completed handbook sections. Streamline administrative tasks. In addition to the basic recordkeeping tasks, the Windows App enables secretaries to efficiently handle fees and payments, track inventory and orders, analyze. The Approved Workman database software is designed to help club secretaries reduce their record-keeping burden, and to help leaders spend more of their precious time in ministry to kids instead of completing paperwork. The database lets you easily transition from an inefficient paper-based record-keeping system to a streamlined program on a laptop or desktop computer.
Leaders/listeners can use the Web App on their smartphones, tablets, Mac or Windows PCs to record clubber attendance and mark completed handbook sections. Streamline administrative tasks. In addition to the basic recordkeeping tasks, the Windows App enables secretaries to efficiently handle fees and payments, track inventory and orders, analyze. The Approved Workman database software is designed to help club secretaries reduce their record-keeping burden, and to help leaders spend more of their precious time in ministry to kids instead of completing paperwork. The database lets you easily transition from an inefficient paper-based record-keeping system to a streamlined program on a laptop or desktop computer.
For more information about security, see the Apple Product Security page.
macOS Mojave 10.14.6, Security Update 2019-004 High Sierra, Security Update 2019-004 Sierra
Released July 22, 2019
AppleGraphicsControl
Available for: macOS Mojave 10.14.5
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8693: Arash Tohidi of Solita
autofs
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: Extracting a zip file containing a symbolic link to an endpoint in an NFS mount that is attacker controlled may bypass Gatekeeper
Description: This was addressed with additional checks by Gatekeeper on files mounted through a network share.
CVE-2019-8656: Filippo Cavallarin
Bluetooth
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2018-19860
Bluetooth
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An attacker in a privileged network position may be able to intercept Bluetooth traffic (Key Negotiation of Bluetooth - KNOB)
Description: An input validation issue existed in Bluetooth. This issue was addressed with improved input validation.
CVE-2019-9506: Daniele Antonioli of SUTD, Singapore, Dr. Nils Ole Tippenhauer of CISPA, Germany, and Prof. Kasper Rasmussen of University of Oxford, England
The changes for this issue mitigate CVE-2020-10135.
Entry added August 13, 2019, updated June 25, 2020
Carbon Core
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A use after free issue was addressed with improved memory management.
CVE-2019-8661: Natalie Silvanovich of Google Project Zero
Core Data
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8646: Natalie Silvanovich of Google Project Zero
Core Data
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause unexpected application termination or arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8660: Samuel Groß and Natalie Silvanovich of Google Project Zero
CUPS
Available for: macOS Sierra 10.12.6, macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An attacker in a privileged network position may be able to execute arbitrary code
Description: A buffer overflow issue was addressed with improved memory handling.
CVE-2019-8675: Stephan Zeisberg (github.com/stze) of Security Research Labs (srlabs.de)
CVE-2019-8696: Stephan Zeisberg (github.com/stze) of Security Research Labs (srlabs.de)
Entry added August 14, 2019, updated September 17, 2019
Disk Management
Available for: macOS Mojave 10.14.5
Impact: A malicious application may be able to execute arbitrary code with system privileges
Description: A memory initialization issue was addressed with improved memory handling.
CVE-2019-8539: ccpwd working with Trend Micro's Zero Day Initiative
Entry added September 17, 2019
Disk Management
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
Sep 30, 2019 Google Drive is a compelling choice because it offers 15 GB of storage space, and best-in-class web apps, like Google Docs and Sheets for free. Dropbox (also free) is a good choice if you don’t need the attached web services and prefer a simpler, leaner (2 GB) cloud storage service. Apr 15, 2020 That said, no matter how avid a Mac user you are, I can bet that you will find new Mac apps in this article that you have never heard of before. So, open your Macs and get ready to download these awesome free Mac apps. Note: Be sure to read our must-have iPhone apps article to get the best apps for your iPhone in 2020. Stay on top of today's fast-changing Apple technology with Macworld magazine! Macworld is the ultimate resource for savvy users of Apple products. Every issue is filled with authoritative news, analysis, and tips about all things Apple - Mac, iPhone, iPad, and beyond! Best of all, Macworld. 
CVE-2019-8697: ccpwd working with Trend Micro’s Zero Day Initiative
FaceTime
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to cause arbitrary code execution
Description: A memory corruption issue was addressed with improved input validation.
CVE-2019-8648: Tao Huang and Tielei Wang of Team Pangu
Found in Apps
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: This issue was addressed with improved checks.
CVE-2019-8663: Natalie Silvanovich of Google Project Zero
Game Center
Available for: macOS Mojave 10.14.5
Impact: A local user may be able to read a persistent account identifier
Description: This issue was addressed with a new entitlement.
CVE-2019-8702: Min (Spark) Zheng and Xiaolong Bai of Alibaba Inc.
Entry added February 24, 2020
Grapher
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8695: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
Graphics Drivers
Available for: macOS Mojave 10.14.5, macOS High Sierra 10.13.6
Impact: An application may be able to read restricted memory
Description: A validation issue was addressed with improved input sanitization.
CVE-2019-8691: Aleksandr Tarasikov (@astarasikov), Arash Tohidi of Solita, Lilang Wu and Moony Li of Trend Micro's Mobile Security Research Team working with Trend Micro's Zero Day Initiative
CVE-2019-8692: Lilang Wu and Moony Li of Trend Micro Mobile Security Research Team working with Trend Micro's Zero Day Initiative
Entry updated July 25, 2019
Heimdal
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: An issue existed in Samba that may allow attackers to perform unauthorized actions by intercepting communications between services
Description: This issue was addressed with improved checks to prevent unauthorized actions.
CVE-2018-16860: Isaac Boukris and Andrew Bartlett of the Samba Team and Catalyst
IOAcceleratorFamily
Available for: macOS Mojave 10.14.5
Impact: An application may be able to execute arbitrary code with kernel privileges

Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8694: Arash Tohidi of Solita
libxslt
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: A remote attacker may be able to view sensitive information
Description: A stack overflow was addressed with improved input validation.
CVE-2019-13118: found by OSS-Fuzz
Quick Look
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: An attacker may be able to trigger a use-after-free in an application deserializing an untrusted NSDictionary
Description: This issue was addressed with improved checks.
CVE-2019-8662: Natalie Silvanovich and Samuel Groß of Google Project Zero
Safari
Available for: macOS Mojave 10.14.5
Impact: Visiting a malicious website may lead to address bar spoofing
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2019-8670: Tsubasa FUJII (@reinforchu)
Security
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8697: ccpwd working with Trend Micro’s Zero Day Initiative
sips
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6
Impact: An application may be able to execute arbitrary code with system privileges
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2019-8701: Simon Huang(@HuangShaomang), Rong Fan(@fanrong1992) and pjf of IceSword Lab of Qihoo 360
Entry added October 8, 2019
Siri
Available for: macOS Mojave 10.14.5
Impact: A remote attacker may be able to leak memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8646: Natalie Silvanovich of Google Project Zero
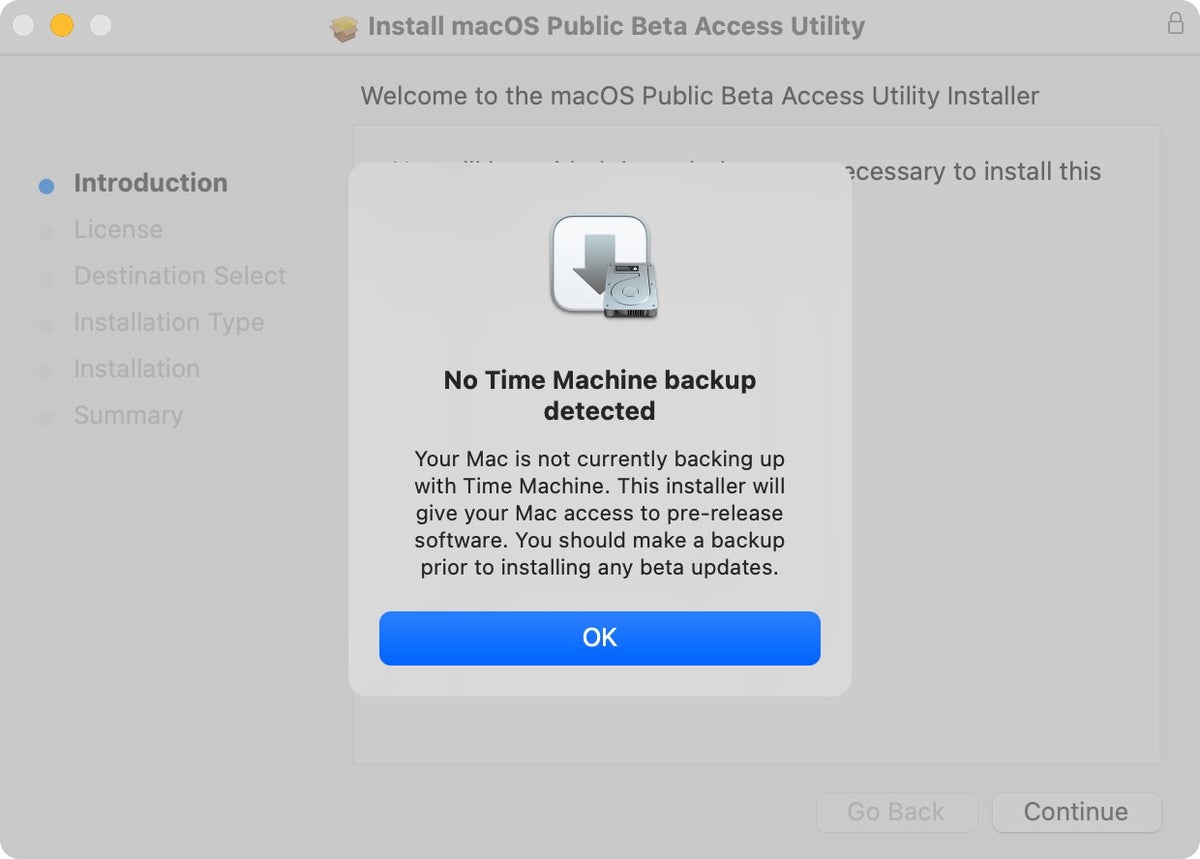
Time Machine
Available for: macOS Mojave 10.14.5
Impact: The encryption status of a Time Machine backup may be incorrect
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2019-8667: Roland Kletzing of cyber:con GmbH
UIFoundation
Available for: macOS Sierra 10.12.6, macOS High Sierra 10.13.6, macOS Mojave 10.14.5
Impact: Parsing a maliciously crafted office document may lead to an unexpected application termination or arbitrary code execution
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2019-8657: riusksk of VulWar Corp working with Trend Micro's Zero Day Initiative
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of document loads. This issue was addressed with improved state management.
CVE-2019-8690: Sergei Glazunov of Google Project Zero
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of synchronous page loads. This issue was addressed with improved state management.
CVE-2019-8649: Sergei Glazunov of Google Project Zero
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue was addressed with improved state management.
CVE-2019-8658: akayn working with Trend Micro's Zero Day Initiative
WebKit
Available for: macOS Mojave 10.14.5
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2019-8644: G. Geshev working with Trend Micro's Zero Day Initiative
CVE-2019-8666: Zongming Wang (王宗明) and Zhe Jin (金哲) from Chengdu Security Response Center of Qihoo 360 Technology Co. Ltd.
CVE-2019-8669: akayn working with Trend Micro's Zero Day Initiative
CVE-2019-8671: Apple
CVE-2019-8672: Samuel Groß of Google Project Zero
CVE-2019-8673: Soyeon Park and Wen Xu of SSLab at Georgia Tech
CVE-2019-8676: Soyeon Park and Wen Xu of SSLab at Georgia Tech
CVE-2019-8677: Jihui Lu of Tencent KeenLab
CVE-2019-8678: an anonymous researcher, Anthony Lai (@darkfloyd1014) of Knownsec, Ken Wong (@wwkenwong) of VXRL, Jeonghoon Shin (@singi21a) of Theori, Johnny Yu (@straight_blast) of VX Browser Exploitation Group, Chris Chan (@dr4g0nfl4me) of VX Browser Exploitation Group, Phil Mok (@shadyhamsters) of VX Browser Exploitation Group, Alan Ho (@alan_h0) of Knownsec, Byron Wai of VX Browser Exploitation
CVE-2019-8679: Jihui Lu of Tencent KeenLab
CVE-2019-8680: Jihui Lu of Tencent KeenLab
CVE-2019-8681: G. Geshev working with Trend Micro Zero Day Initiative
CVE-2019-8683: lokihardt of Google Project Zero
CVE-2019-8684: lokihardt of Google Project Zero
CVE-2019-8685: akayn, Dongzhuo Zhao working with ADLab of Venustech, Ken Wong (@wwkenwong) of VXRL, Anthony Lai (@darkfloyd1014) of VXRL, and Eric Lung (@Khlung1) of VXRL
CVE-2019-8686: G. Geshev working with Trend Micro's Zero Day Initiative
CVE-2019-8687: Apple
CVE-2019-8688: Insu Yun of SSLab at Georgia Tech
CVE-2019-8689: lokihardt of Google Project Zero
Additional recognition
Classroom
We would like to acknowledge Jeff Johnson of underpassapp.com for their assistance.
Game Center
We would like to acknowledge Min (Spark) Zheng and Xiaolong Bai of Alibaba Inc. for their assistance.
This is a series of tips that cover Mac OS X client edition. Server forums cover Mac OS X server on the community.
Here is the series of tips for related Macs. 10.6,10.7, 10.8, 10.9, 10.10,10.11,
10.12 ,10.13, 10.14 Mojave, 10.15 Catalina.
See special note about resetting the SMC during updates and upgrades, later in the tip.
is an article I wrote that everyone updating their Mac should read. No update should be ventured into with operating systems or software without first ensuring your data is backed up in two separate places. Slowing down of your Mac should not lead you to assume an update will fix everything. First isolate why your Mac is slowing down or crashing before installing anything new.
Apple released for 10.14.6 users, 2020-003 Mojave security update. If running an earlier version of 10.14, run the 10.14.6 Combo update first.
Apple recommends you have these Macs according to: https://support.apple.com/kb/SP777?locale=en_US
- MacBook (Early 2015 or newer) [model identifier 8,1 or later]
- MacBook Air (Mid 2012 or newer) [model identifier 5,1 or later]
- MacBook Pro (Mid 2012 or newer) [model identifier 9,1 or later]
- Mac mini (Late 2012 or newer) [model identifier 6,1 or later]
- iMac (Late 2012 or newer) [model identifier 12,1 or later]
- Mac Pro (Late 2013; Mid 2010 and Mid 2012 models with recommended Metal-capable graphics cards) [model identifier 5,1 or later]
bracketed items in quotes were added for additional identification purposes. Your Apple menu -> About This Mac -> System Report or System Profiler gives you the model identifier.
All of the Macs that are older than 10.11, need to be updated to 10.11 first before installing Mojave.
The oldest MacBook Air, Mac mini, and iMac which can upgrade to Mojave shipped with 10.8, Mountain Lion.
The oldest MacBook Pro which can upgrade to Mojave shipped with 10.7, Lion.
Macos 10.14.6 This Software Is Not Supported Video
The oldest MacBook had Mac OS X 10.10 installed.
The oldest Mac Pro on the list above with the compatible graphics cards, had 10.6 originally installed, and is the only Mac that shipped with 10.6 that can install Mojave. Before upgrading to 10.7 or later, read this tip as Apple has not reintroduced a series of software that made older Mac compatible software compatible with Intel Macs since 10.6.8's release.
Apple released Mojave on September 24, 2018. Reports from:
earlier than that date were made with pre-release Mojave versions and can not be relied upon.
Macos 10.14.6 This Software Is Not Supported Free
September 30, 2018 driver additions from third party update pages:
HP, and Samsung (HP has become the download site for at least some Mojave Samsung printers, if you have Samsung see if any are Catalina compatible)
Silverfast.
10.14.3 was released January 22, 2019. Note, some users are reporting 10.14.3 will not successfully apply as an update without an SMC reset as described how to do in this link: https://support.apple.com/en-us/HT201295
Frequently both updates and upgrades will require multiple reboots to successfully apply. Do NOT become impatient if you find the screen go blank during the update or upgrade process. If you press the power button to shut it down while it is rebooting for the update or upgrade, it may quit the process, and leave you stuck.
Macos 10.14.6 This Software Is Not Supported Youtube
Use the macOS Mojave forum for operating system specific questions of other end users such as yourself.
Note: https://support.apple.com/guide/disk-utility/partition-a-physical-disk-dskutl14027/mac
Macos 10.14.6 This Software Is Not Supported Iphone
are directions for creating a separate partition that will allow you to dual boot into an older operating system
if you find something not compatible with the current. Once you install the older operating system, you can use the Startup manager to dual boot to the older system.
You can't install Mojave from the Finder, unless you are running 10.13.6 or earlier.
The direct download link for Mojave is:
Note: some people have had trouble downloading the latest Mojave links. https://brave.com/ has been found to be a better web browser than some if you run into issues and is known to work on Mac OS X 10.10 and later.
Unsupported Macs may have Mojave installed with a patch from http://dosdude1.com/mojave/
This is at your own risk. Follow the directions given by the patch author.